Key Takeaways
- Understand how VPN split tunneling can enhance your internet experience
- Identify the potential risks and how to mitigate them
- Learn practical tips for effective implementation
Why VPN Split Tunneling Matters
In today’s fast-paced digital landscape, the demand for reliable and fast internet connectivity is higher than ever. With the global shift towards remote work and the exponential growth of online activities, managing internet traffic efficiently has become critical. This is where VPN split tunneling comes into play, offering a nuanced approach to connectivity. By allowing users to delineate which data travels via a VPN and which connects directly to the internet, split tunneling optimizes both speed and security. This technique is vital for those dealing with bandwidth-intensive applications and services, as it enables faster data transmission by avoiding the unnecessary slowdowns that come with routing all traffic through a VPN. The forward-thinking nature of split tunneling makes it a fundamental tool for anyone serious about maximizing digital efficiency without compromising safety.
How Does VPN Split Tunneling Work?
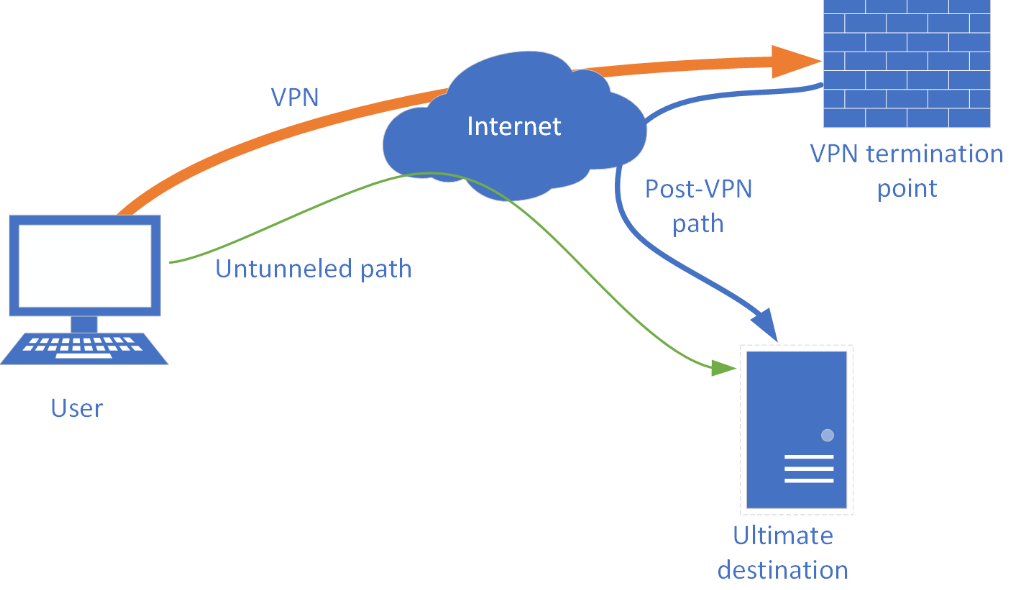
The functionality of VPN split tunneling is intriguingly straightforward yet fundamentally transformative for managing online activities. In a traditional VPN setup, all traffic goes through a secure, encrypted tunnel, which, while safeguarding data, often slows down the overall connection due to increased load. With split tunneling, users gain control by choosing specific traffic through the VPN, keeping the rest on the open internet. This selective routing harnesses the security of a VPN for sensitive tasks, like accessing company databases, while permitting less critical activities, such as general browsing or video streaming, to bypass the VPN firewall. Such flexibility allows network architects to calibrate resources precisely, ensuring priority access where needed while significantly alleviating unnecessary congestion and enhancing user experience.
Benefits of Using VPN Split Tunneling
- Improved Internet Speed: One of the primary advantages of split tunneling is the remarkable improvement in internet speed. Segregating protected and unprotected traffic reduces the load on the VPN, making bandwidth-intensive activities smooth and fast. This capability is a game-changer for users who engage in tasks that require high-speed connections, such as live streaming, gaming, and large file transfers. Reducing latency and buffering issues transforms user interactions with digital content, offering a seamless and engaging experience.
- Bandwidth Optimization: Efficient bandwidth management is crucial, especially for organizations with extensive digital infrastructure. Split tunneling provides an innovative approach to optimizing bandwidth by preventing unnecessary data from clogging the VPN. This selective data handling ensures that only critical business operations utilize secure VPN pathways, freeing up significant bandwidth for other activities. Such optimization not only enhances operational efficiency but also reduces costs associated with bandwidth overconsumption.
- Access to Local and Foreign Resources: Another significant benefit of VPN split tunneling is its ability to provide dual connectivity. This feature is particularly advantageous for users who need simultaneous access to local and foreign resources. For instance, employees can print documents to a local printer while their system remains connected to overseas servers. This dual-access capability is invaluable for streamlining workflows and increasing productivity by removing the friction of switching between protected and unprotected networks.
Potential Risks and Concerns
While VPN split tunneling offers various advantages, it’s imperative to consider its risks. One potential issue is the exposure of unencrypted traffic to cyber threats, which can lead to data breaches if not adequately managed. The partial routing inherent in split tunneling can allow unauthorized access to sensitive information. Therefore, organizations must implement rigorous security measures to mitigate these threats. Experts from CSO Online emphasize the importance of endpoint security, continuous updates, and user education to ensure safe browsing practices. By carefully balancing ease of access with comprehensive security protocols, users can enjoy the benefits of split tunneling while minimizing potential vulnerabilities.
Practical Implementation Tips
- Choosing the Right VPN Provider: Selecting a VPN provider that supports split tunneling is essential. Not all services offer this feature, so choosing one that does and provides strong security measures and flexible configuration options is necessary. Look for providers with intuitive interfaces and detailed setup instructions to ensure a seamless implementation process.
- Configuring Your Settings Correctly: Proper configuration is the foundation of a successful split tunneling implementation. Evaluate which data types require VPN encryption and customize your settings accordingly. This step ensures that sensitive traffic is protected while other activities are not hindered by unnecessary encryption, thus maximizing speed and security simultaneously.
- Regular Audits and Monitoring: Continuous surveillance of network traffic is essential to maintain the integrity of a split tunneling setup. Conducting regular audits helps identify unauthorized access attempts or unusual activities, allowing for prompt corrective actions. Deploying tools with real-time threat alerts and detailed logs can further fortify network defenses, ensuring robust and comprehensive security.
Future Trends in VPN Technology
As technology continues to evolve, VPN solutions are adapting to meet increasingly sophisticated digital demands. Future trends indicate that VPNs will become even more dynamic, offering enhanced performance, scalability, and security features. Such evolution is especially pertinent as hybrid and remote work models become standard for business operations—websites like TechCrunch detail how advancements in cybersecurity are reshaping VPN technologies. Staying abreast of these trends is crucial for users and organizations aiming to leverage the full potential of VPN split tunneling and similar technologies. As innovation pushes boundaries, being informed can ensure your networks remain resilient, agile, and future-proof.
Conclusion: Weighing Pros and Cons
VPN split tunneling represents a significant leap forward in balancing internet efficiency and security. Its speed and resource management benefits are substantial but must be aligned with solid security practices to avoid potential pitfalls. Users can optimize their digital environments by understanding their network’s specific needs and carefully considering the implementation of split tunneling. The key lies in crafting a personalized strategy that leverages the strengths of split tunneling while mitigating its risks, ensuring a secure and efficient online experience that meets current and future needs.